All incidents were accompanied by the distribution of fake emails to the addresses of the targeted organizations. Malicious documents were disguised as legitimate Microsoft Windows elements. In particular, the emails sent in September appeared as messages from potential clients inquiring about mobile tariff rates.
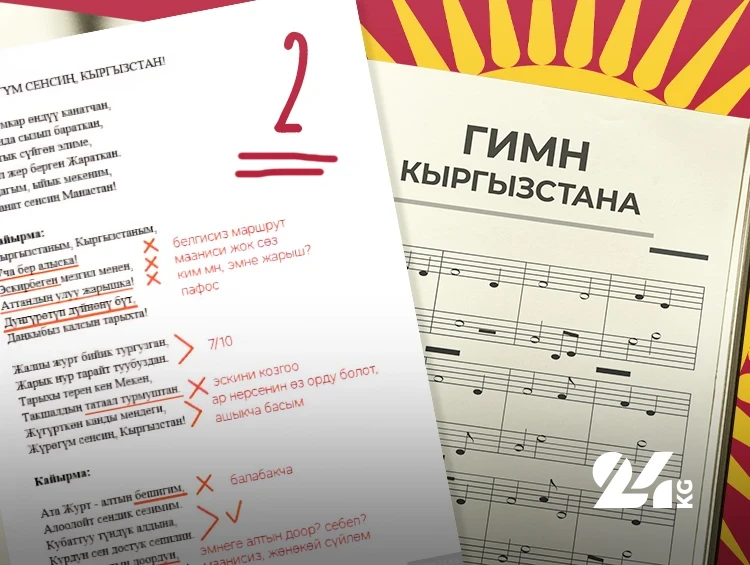
When users opened the attachments, they saw an image containing a request to activate macros. After this operation, to divert attention, a tariff plan (borrowed from another provider) was displayed, while in reality, a targeted malicious code was being installed.
Analysis revealed that the backdoor, loaded by the script (named LuciDoor), was developed in C++ and could connect to C2 both directly and through system proxies and other servers in the victim's network. Its functions include gathering information about the infected device, downloading additional programs, and exfiltrating data.
New attacks on Kyrgyzstan's telecommunications sector were recorded in November. The attackers changed the bait; however, they made the same mistake by using a name that did not match the recipient's address. This time, the Windows backdoor MarsSnake was used, which had previously been observed in espionage attacks in Saudi Arabia.
The MarsSnake backdoor is notable for its simple configuration: changes can be made by updating parameters in the loader, eliminating the need to rebuild the executable file. After installation, the malware collects system data, creates a unique identifier, and sends information to C2.
“Interestingly, in last year's attacks, the malicious documents were in Russian, while the settings used Arabic, English, and Chinese languages,” noted PT ESC TI specialist Alexander Badaev. “We also found a field in the files indicating the use of the Chinese language. It is possible that the attackers used a Microsoft Office package with the corresponding settings or applied a document template in Chinese.”
In the January attacks on Tajikistan, links were used instead of malicious attachments. The image with the request to activate macros was redesigned, and the text was in English. The targeted malware was again LuciDoor, but in a different configuration.